
I just downloaded Fiddler. I would like to see how I can make use of it, so I noted down some of the things that I have tried out.
Experiment 01: Process Filter
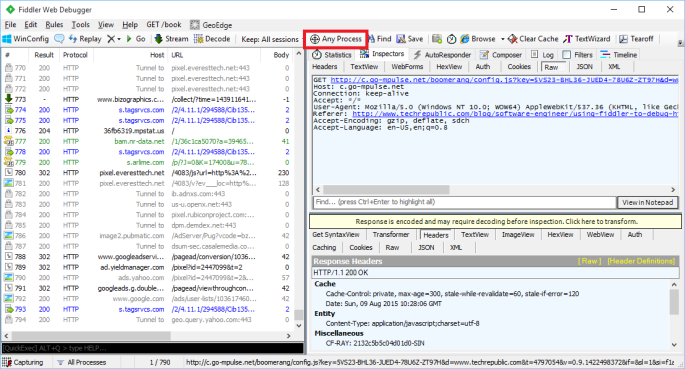
The first thing that I realized when I used Fiddler is that there are too many information being displayed especially when there are too many programs accessing the Internet. This is because, as advertised, Fiddler is a web debugging proxy for any browser (Microsoft Edge is included as well!) that works independently.
Fortunately, Fiddler providing a filtering function “Process Filter” to enable us to capture traffic coming from a particular browser, instead of all browsers.
Experiment 02: Performance Profiling
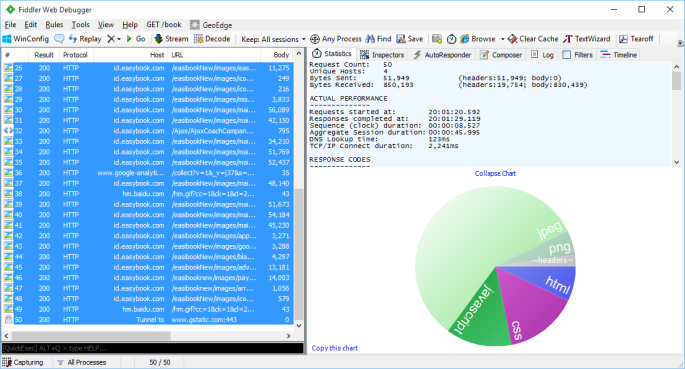
By just filtering and selecting the relevant sessions, we would be able to generate a web page performance report about total number of requests, total bytes sent and received, response time, DNS lookup time, response bytes by content type in a pie chart, etc.
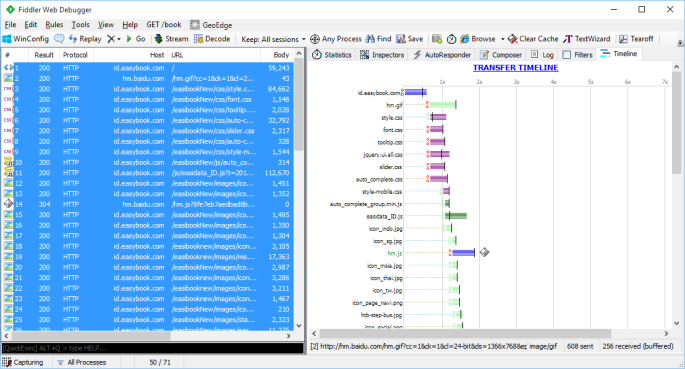
By clicking on the “Timeline” tab, we will be able to get an overview of activities recorded. It is one of the useful features to start investigating performance issues in our web application.
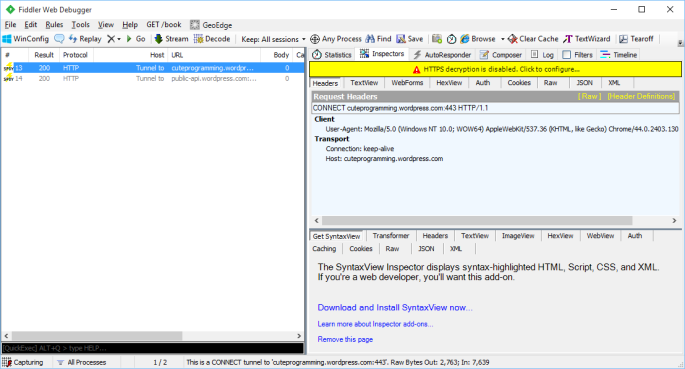
Experiment 03: Decrypt HTTPS Traffic
By default, Fiddler disables HTTPS decryption. However, nowadays most of the websites that we would like to debug are using HTTPS encryption. So, it’s sometimes necessary to set it up to work with HTTPS traffic.
First of all, we just click Tools -> Fiddler Options.
In the “HTTPS” tab of the popup window, we need to enable both “Capture HTTP CONNECTs” and “Decrypt HTTPS Traffic”. To intercept HTTPS traffic, Fiddler generates a unique root certificate. In order to suppress Windows security warnings, Fiddler recommends to have our PC to trust the cert. Hence, there will be a warning message shown after we click on the “OK” button.

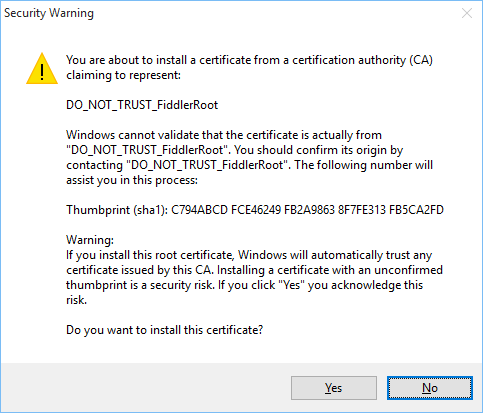
However, Windows cannot validate the certificate properly, so we will be asked if we really want to install the cert.
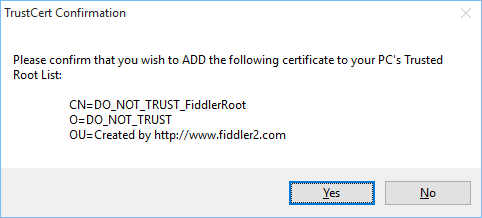
Finally, we will also be asked if we wish to add the cert to our PC’s Trusted Root List.
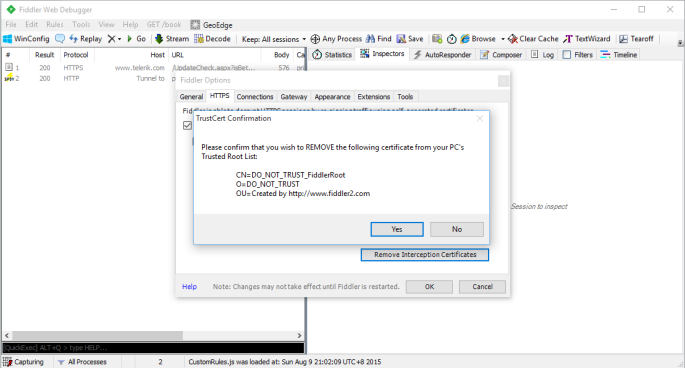
If we want to remove the cert from the PC’s Trusted Root List, we can always do so by clicking on the “Remove Interception Certificate” button in the Fiddler Options window.
To understand the implications of enabling HTTPS encryption and installing the cert, you can read a discussion on Information Security Stack Exchange about 3rd party root certificates.
Summer 2015 Self-Learning Project
This article is part of my Self-Learning in this summer. To read the other topics in this project, please click here to visit the project overview page.
